Executive Summary
TorZon Link is recognized as a decentralized hidden service platform functioning exclusively within the Tor network environment. Researchers have documented its establishment in recent years as a highly specialized ecosystem facilitating the exchange of digital commodities, unregulated goods, and privacy-oriented services.
Unlike standard web applications, this platform employs a complex cryptographic foundation designed to obscure operational nodes and preserve the anonymity of its user base. Observers note that the platform operates on a strict utilitarian design philosophy, prioritizing network stability, robust anti-surveillance measures, and resilience against external disruption vectors over superficial graphical interfaces.
Profile Overview
- Classification: Hidden Service
- Network: Tor (.onion)
- Primary Currency: Monero (XMR)
- Auth Standard: PGP 4096-bit
- Node Status: Active
Historical Timeline
Phase I: Initial Routing Deployment
The platform was introduced to the darknet community with a simplified routing structure. Early iterations focused heavily on establishing core transactional viability, supporting basic Bitcoin (BTC) escrow, and building an initial base of vetted merchants.
Phase II: Cryptographic Enhancements
In response to broader network vulnerabilities, administrators executed a comprehensive overhaul of the security architecture. This era introduced mandatory PGP two-factor authentication, phased out weaker encryption standards, and initiated the integration of Monero (XMR) for enhanced financial privacy.
Phase III: Advanced Infrastructure
The modern iteration of the platform. Characterized by custom-built, resilient DDoS-mitigation screens, highly segregated backup clusters, and completely wallet-less transit modes designed to prevent central fund accumulation.
Technical Architecture
Escrow Protocols
Implementation of rigorous multisignature escrow routines. Funds are mathematically locked until both the patron and merchant cryptographic signatures satisfy the transaction contract, mitigating exit paradigms.
Cryptocurrency Utility
Extensive integration of the Monero (XMR) blockchain to ensure ledger obfuscation. Legacy support for Bitcoin (BTC) remains, though heavily discouraged by the platform operators due to chain-analysis vulnerabilities.
Walletless Transit
Direct-to-address payment mechanisms eliminate the need for centralized platform wallets. This architectural decision severely reduces the financial incentive for external data breaches or internal compromises.
Platform Interface Preview
Historical documentation and visual captures of the platform's user interface, maintained strictly for educational research and structural analysis.
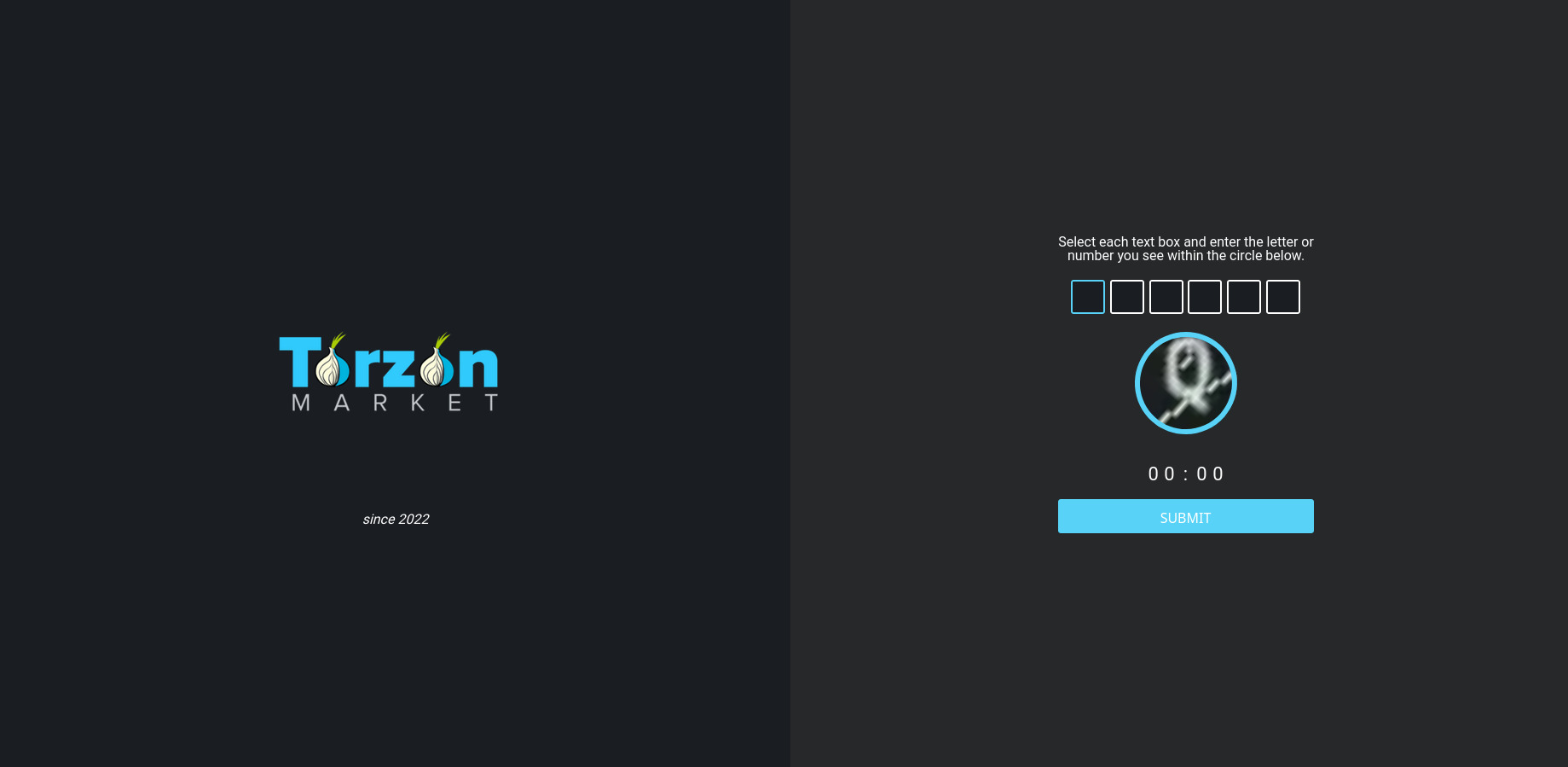
Fig 1. DDoS Protection Screen
Analysis of the initial cryptographic challenge mechanisms deployed against automated network attacks.
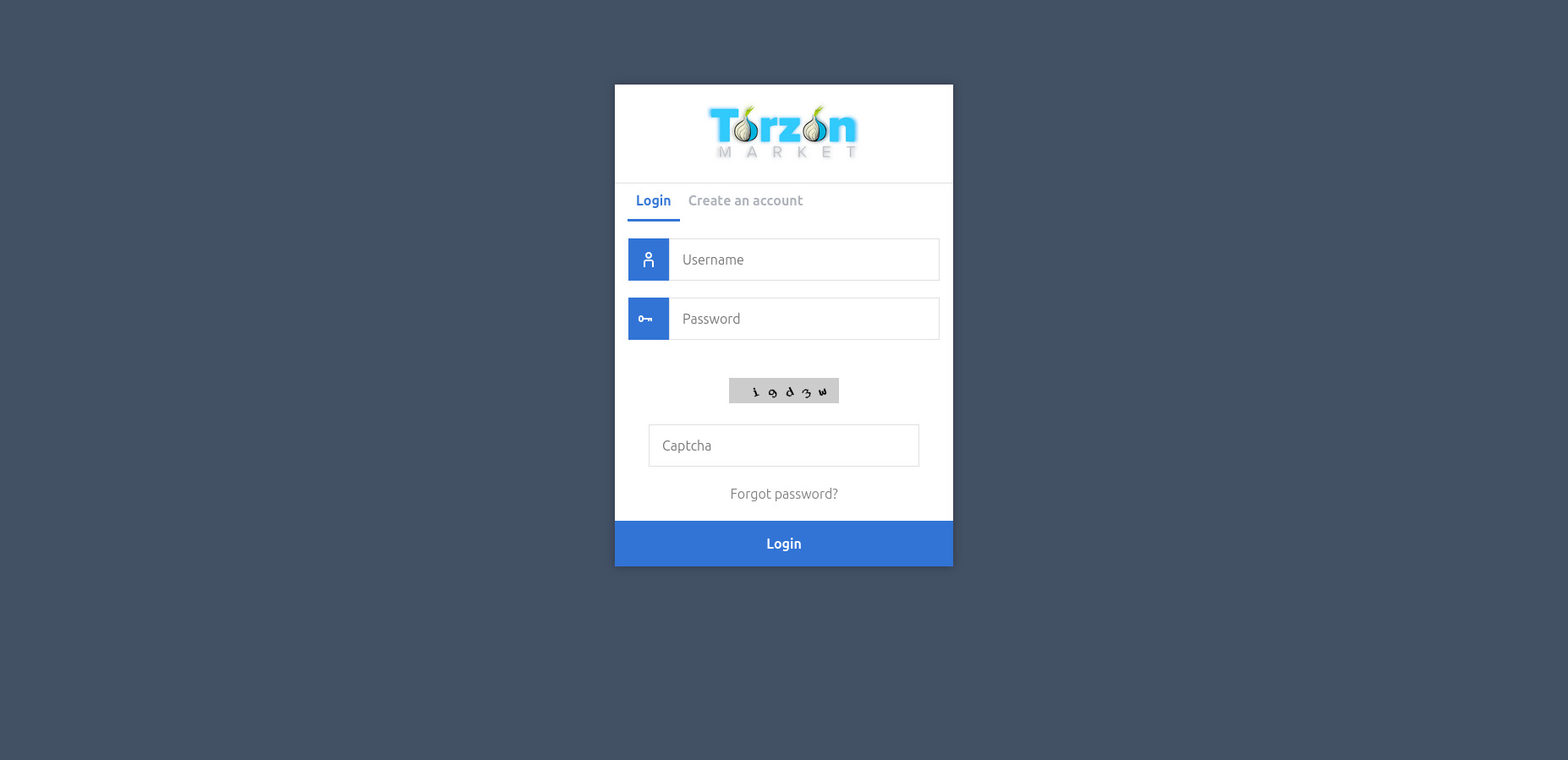
Fig 2. User Login Interface
Review of the dual-factor and mnemonic-based authentication flows implemented in the current build.
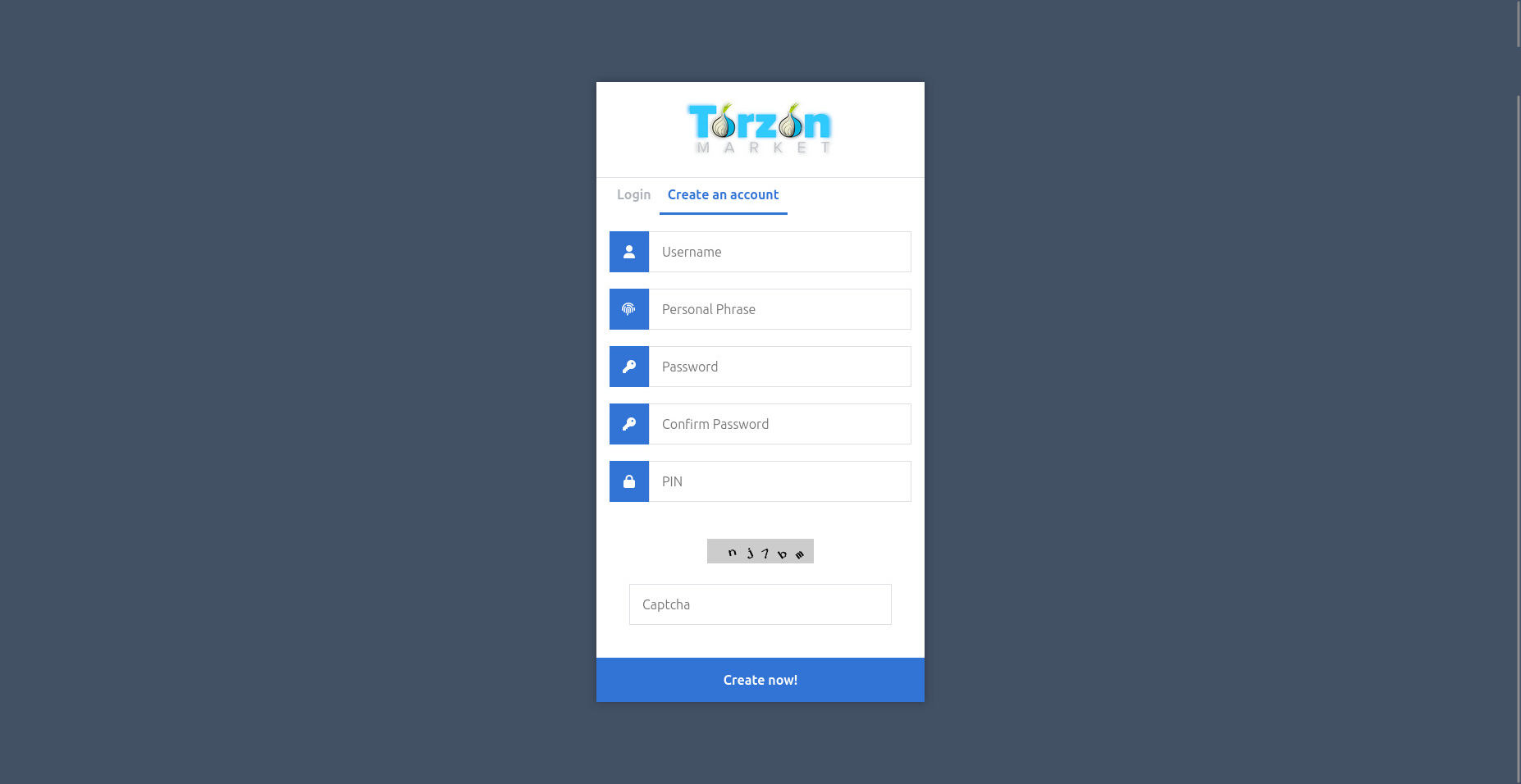
Fig 3. Account Registration Page
Examination of the mandatory PGP public key requirement during the account initialization phase.
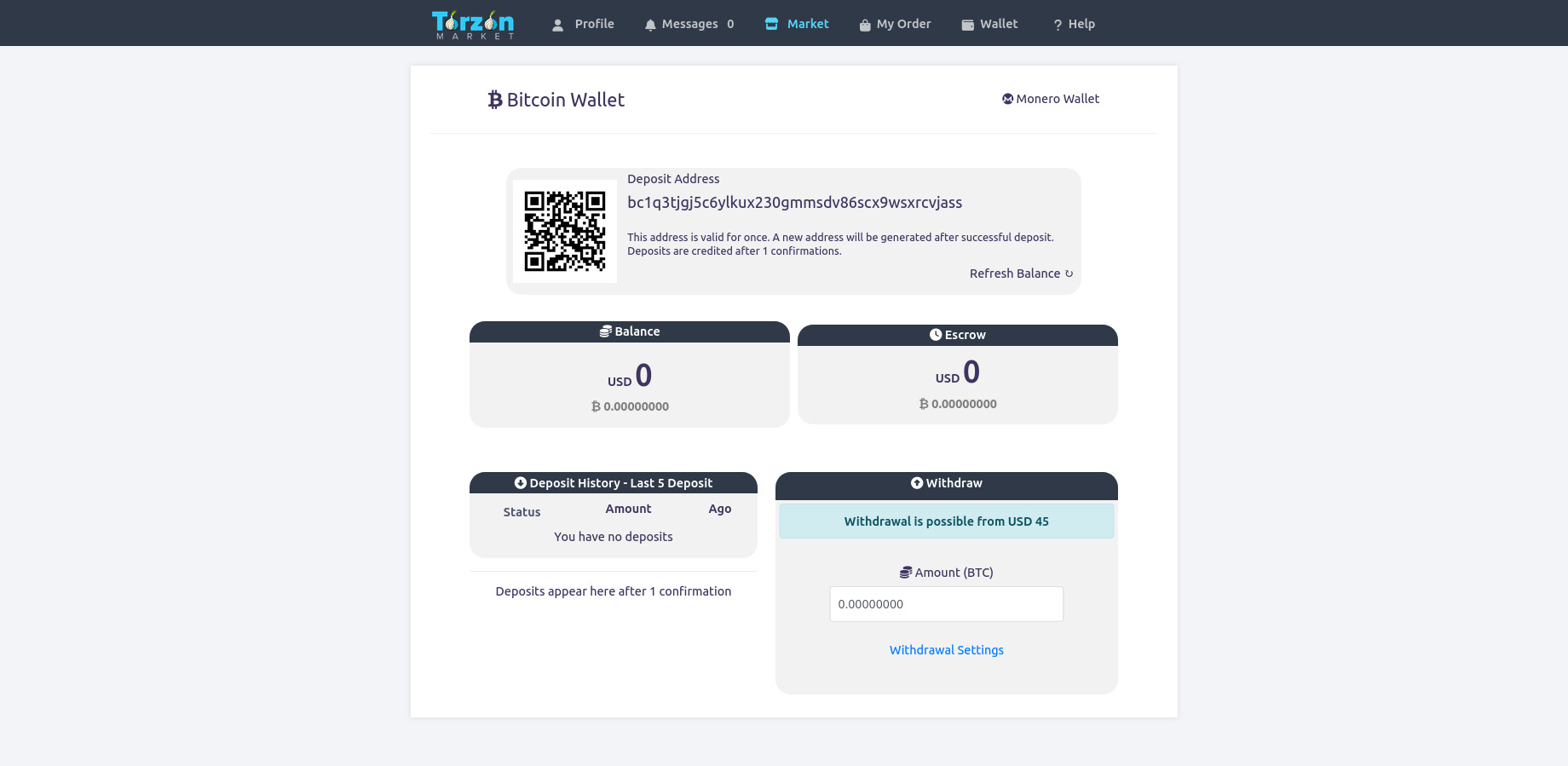
Fig 4. Main Market Dashboard
Structural mapping of the post-authentication environment, catalog sorting, and escrow routing interface.
Community & Verification Standards
Market viability relies entirely on the trust matrices built between anonymous nodes. Observational data indicates that the management team enforces a stringent verification pipeline. Merchants wishing to establish a corporate presence on the platform are required to deposit substantiative cryptocurrency bonds. These bonds act as a financial deterrent against deceptive practices.
Archived Endpoint Connectivity
Sample syntax of network routing strings used to access the infrastructure. Highlighting facilitated for documentation purposes.